Someone took my bytes! Can you recover my password for me?
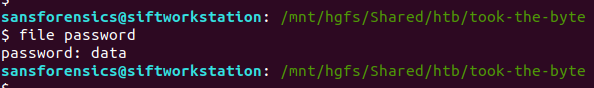
This time all we are given is a single file named password, which is identified simply as data.
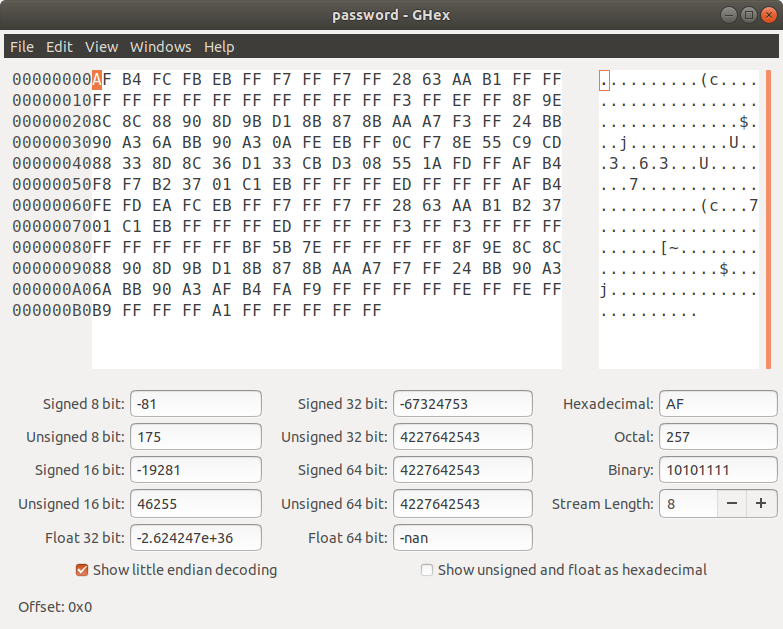
Examining it in a hex editor doesn’t give many more clues.
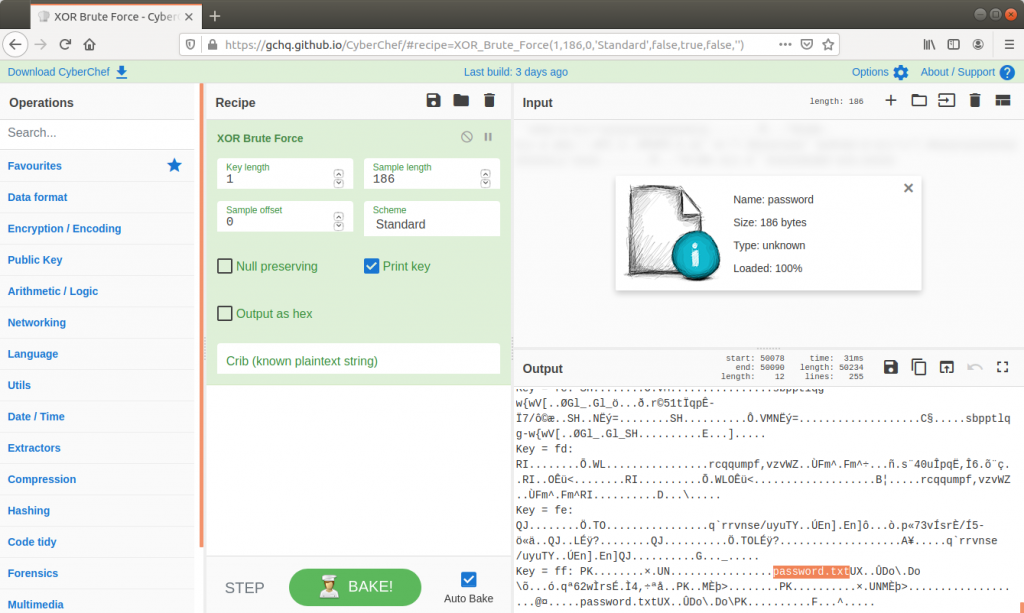
I began thinking that the data might be encrypted somehow, and threw it into CyberChef.
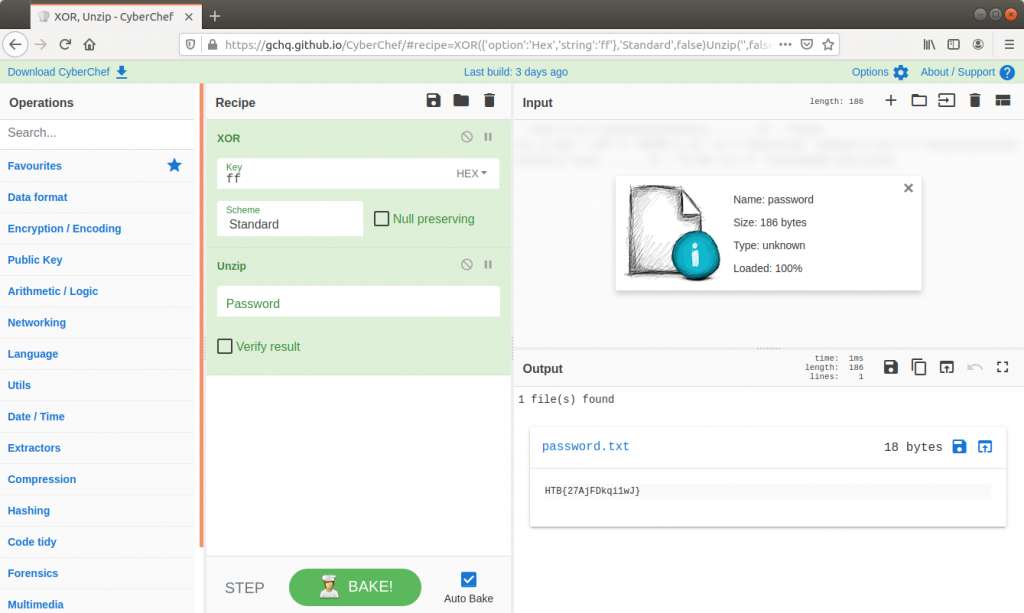
Using the XOR Brute Force module with the default key length of 1 byte, I noticed that using 0xff as a key output a PK header associated with a ZIP archive which appeared to contain a file named password.txt. Quickly building a new recipe, I used the standard XOR module to decrypt the data using key 0xff, then used the Unzip module to extract and view the contents of password.txt which contains our flag.
Flag
HTB{27AjFDkqi1wJ}
1 thoughts on “Hack The Box – Took the Byte (Forensics Challenge)”